Blog

Summer is the perfect time to get the most out of your MOREnet Membership Service Package benefits.
Schedule an assessment
Both Cybersecurity Assessments and Network Assessments are included with your Full Membership Service Package. With both assessments,...

Are You Watching The Watchers?
Managed Service Providers (MSP) are a critical component for managing networks for many organizations. Due to lack of personnel or expertise, institutions are...

AI TRiSM
With the emergence of Artificial Intelligence (AI) the landscape of trust and security needs to be considered. Thus, the development of, yet another...

Verizon 2023 Data Breach Investigation Report
Verizon's annual Data Breach Investigation Report (DBIR) is out! Key takeaways indicate that social engineering attacks using (BEC) Business Email Compromise have almost...

What is a Vulnerability?
A vulnerability, in information technology (IT), is a flaw in code or design that creates a potential point of security compromise for an...

It's NOT Security Awareness Training
Fingernails on a chalk board. That is what this term sounds like to me. I believe awareness is a result of education. Training...

Is Your Connected Home Telling Your Secrets?
As the Internet of Things (IoT) continues to evolve, users are expanding their home networks to include these new devices. Most of these...
Secure Password Strategies
The foundation to secure passwords strategies is having a strong password. What makes a strong password? Longer=stronger. Even with two-factor/multi-factor (2FA/MFA) implementations, getting...

ChatGPT and a Dozen (or so) things you can do with it.
Obviously ChatGPT has been taking the media by storm and we aren't quite sure what to do with it. Do we use it...

Access is a Privilege, Not a Right
The misuse of privileged access is a dangerous security threat. It can lead to extensive damages within an organization. Everyone on your network...

New and Upgraded Online Research Resources Databases for MOREnet Consortium
We are excited to share with you that we have negotiated added value to the Online Resources included with your MOREnet Membership Service Package! Beginning in the new fiscal year, July 1, 2023, PrepSTEP databases will now be part of your tool kit, and two existing resources will now include additional features.

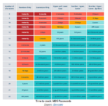
Cybercrime-Trends and Targets
Every day is marred with cyber attacks. Whether it is a data breach, DDoS attack, credential theft or ransomware, these crooks are after...

Ethical Hacking?
When we usually think of hacking, we think of someone sitting in a dark room with a hoodie on, furiously typing away as...

MOREnet Cybersecurity Challenge in National REN Publication
The Quilt is a national coalition of nonprofit regional research and Education Networks (RENs) representing 43 networks across the U.S. As a member of the...

Social Media Spotlight - Chat Rooms
Chat rooms and messaging apps have grown and matured in a way that allows them to stand on their own as another social...

Online Resources Bookmarks
You can find our cyber security screen savers here! We are glad to provide you with these printable bookmarks to remind your stakeholders...

Offsite DNS for Disaster Recovery
Having an offsite DNS server can keep your internet services accessible during outages. As part of your disaster recovery plan, MOREnet can provide offsite DNS for your organization.

World Password Day-May the 4th Be With You
How secure is your password? Is it long and strong? Is it unique for each site or app you log into? Well, if...

E-Rate Training Schedule
We are proud to have the State E-Rate Specialist on staff at MOREnet. Our series of webinars are open to all Missouri schools...

Safe and Secure Disposal of Electronic Devices
Replacing a computer, tablet or network equipment comes with its own set of challenges. Secure configuration before connecting to the network and/or Internet...
